Email Surveillance & Behavior Tracking
MailX delivers proactive monitoring, intelligent analysis, and automated response to defend organizations against email-borne threats.
Real-time Threat Detection
Comprehensive Analysis

Automated Remediation
Integration with Threat Intelligence
Real-Time Monitoring
MailX provides continuous oversight of all inbound and outbound email communications to detect potential threats early. It performs thorough security checks by analyzing
- User Information: Validates sender and recipient identities to spot spoofing or impersonation attempts.
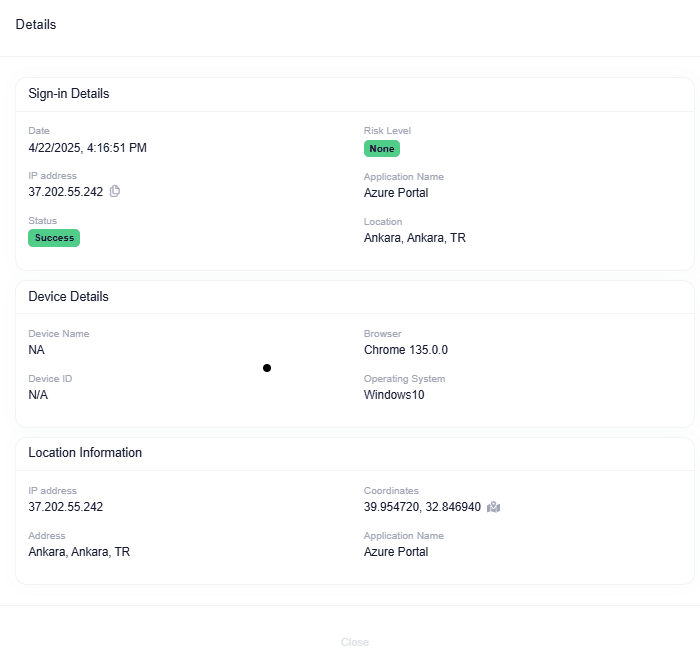
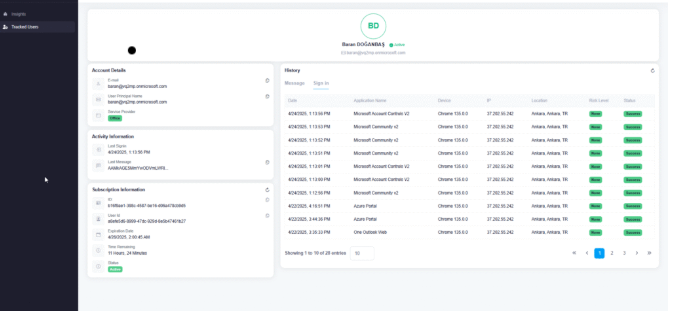
- Login Sessions: Monitors login attempts and session activity to identify unusual behavior.
- Email Content & Headers: Reviews subject lines, body content, and headers for suspicious indicators.
- Links & Attachments: Inspects embedded URLs and file attachments for malware or phishing attempts.
- IP Verification: Confirms sender IP addresses to detect spoofed or suspicious origins.
Sensitive Data Detection: Flags messages containing confidential or sensitive data that could risk exposure
Review and Analysis
Using advanced algorithms and behavioral analysis, MailX identifies anomalies that could signal malicious activity, such as:
- Email Behavior Anomalies:
- Sudden spikes in email volume from new or unfamiliar sources.
- Irregular sending or receiving patterns.
- Content Anomalies:
- Malicious or suspicious links and attachments.
- Keywords or phrases often tied to phishing or fraud.
- User Behavior Anomalies:
- Repeated failed login attempts.
- Excessive password reset requests.
- Activity from dormant or inactive accounts.
- Phishing Indicators:
- Built-in algorithms detect and flag phishing attempts.
Whenever anomalies are detected, MailX instantly notifies administrators or security teams for rapid action.
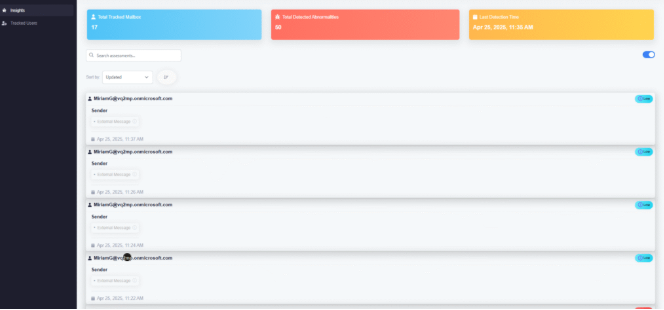
Real-Time Monitoring
MailX actively takes corrective measures to neutralize threats and prevent potential damage. Its remediation features include:
- Incident Sharing: Seamlessly shares detected threat incidents with integrated threat intelligence systems to enable coordinated defense and protection.
- Email Filtering:
- Isolates malicious emails (such as malware, ransomware, or phishing) before they reach users’ inboxes.
- Removes harmful emails from all inboxes to reduce further risk.
- URL Blocking: Uses DNS protection to block access to dangerous websites linked through malicious URLs.
- Sender Blacklisting: Identifies and blocks suspicious or harmful senders, preventing future emails from entering the organization.
- Managed Takedown Services: Initiates takedown actions to eliminate malicious domains or online content from the internet.
Prepared to protect what matters most?
Strengthen your cybersecurity with CYBERONE’s cutting-edge protection solutions. Explore our seamless, easy-to-use tools built to safeguard your digital world.
Quick Links
Contact Us
Contact Info
Phone
+966115121746
sales@cyberone.com.sa